When you deploy MX or Inline, not only can you apply email link isolation to suspicious links in all emails (including benign), you can now also apply email link isolation to all links of a specified disposition. This provides more flexibility in controlling user actions within emails.
For example, you may want to deliver suspicious messages but isolate the links found within them so that users who choose to interact with the links will not accidentally expose your organization to threats. This means your end users are more secure than ever before.
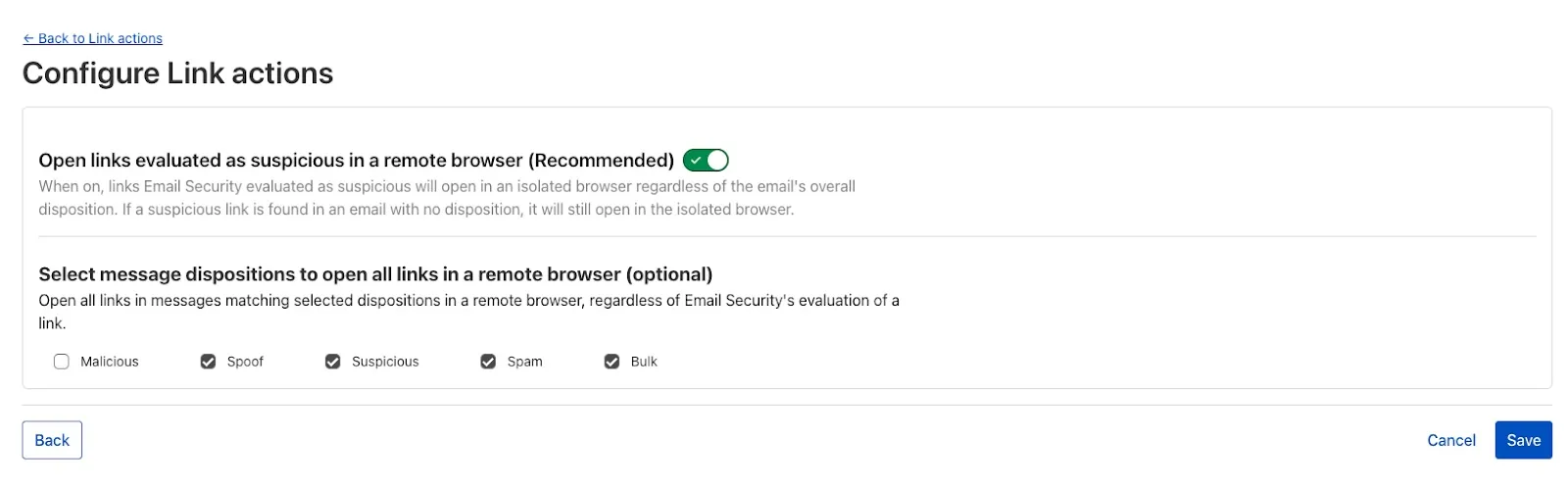
To isolate all links within a message based on the disposition, select Settings > Link Actions > View and select Configure. As with other other links you isolate, an interstitial will be provided to warn users that this site has been isolated and the link will be recrawled live to evaluate if there are any changes in our threat intel. Learn more about this feature on Configure link actions ↗.
This feature is available across these Email security packages:
- Enterprise
- Enterprise + PhishGuard
This week’s highlight focuses on two critical vulnerabilities affecting key infrastructure and enterprise content management platforms. Both flaws present significant remote code execution risks that can be exploited with minimal or no user interaction.
Key Findings
-
Squid (≤6.3) — CVE-2025-54574: A heap buffer overflow occurs when processing Uniform Resource Names (URNs). This vulnerability may allow remote attackers to execute arbitrary code on the server. The issue has been resolved in version 6.4.
-
Adobe AEM (≤6.5.23) — CVE-2025-54253: Due to a misconfiguration, attackers can achieve remote code execution without requiring any user interaction, posing a severe threat to affected deployments.
Impact
Both vulnerabilities expose critical attack vectors that can lead to full server compromise. The Squid heap buffer overflow allows remote code execution by crafting malicious URNs, which can lead to server takeover or denial of service. Given Squid’s widespread use as a caching proxy, this flaw could be exploited to disrupt network traffic or gain footholds inside secure environments.
Adobe AEM’s remote code execution vulnerability enables attackers to run arbitrary code on the content management server without any user involvement. This puts sensitive content, application integrity, and the underlying infrastructure at extreme risk. Exploitation could lead to data theft, defacement, or persistent backdoor installation.
These findings reinforce the urgency of updating to the patched versions — Squid 6.4 and Adobe AEM 6.5.24 or later — and reviewing configurations to prevent exploitation.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100844 Adobe Experience Manager Forms - Remote Code Execution - CVE:CVE-2025-54253 N/A Block This is a New Detection Cloudflare Managed Ruleset 100840 Squid - Buffer Overflow - CVE:CVE-2025-54574 N/A Block This is a New Detection -
By setting the value of the
cacheproperty tono-cache, you can force Cloudflare's cache to revalidate its contents with the origin when making subrequests from Cloudflare Workers.index.js export default {async fetch(req, env, ctx) {const request = new Request("https://cloudflare.com", {cache: "no-cache",});const response = await fetch(request);return response;},};index.ts export default {async fetch(req, env, ctx): Promise<Response> {const request = new Request("https://cloudflare.com", { cache: 'no-cache'});const response = await fetch(request);return response;}} satisfies ExportedHandler<Environment>When
no-cacheis set, the Worker request will first look for a match in Cloudflare's cache, then:- If there is a match, a conditional request is sent to the origin, regardless of whether or not the match is fresh or stale. If the resource has not changed, the cached version is returned. If the resource has changed, it will be downloaded from the origin, updated in the cache, and returned.
- If there is no match, Workers will make a standard request to the origin and cache the response.
This increases compatibility with NPM packages and JavaScript frameworks that rely on setting the
cacheproperty, which is a cross-platform standard part of theRequestinterface. Previously, if you set thecacheproperty onRequestto'no-cache', the Workers runtime threw an exception.- Learn how the Cache works with Cloudflare Workers
- Enable Node.js compatibility for your Cloudflare Worker
- Explore Runtime APIs and Bindings available in Cloudflare Workers
Cloudflare Load Balancing Monitors support loading and applying settings for a specific zone to monitoring requests to origin endpoints. This feature has been migrated to new infrastructure to improve reliability, performance, and accuracy.
All zone monitors have been tested against the new infrastructure. There should be no change to health monitoring results of currently healthy and active pools. Newly created or re-enabled pools may need validation of their monitor zone settings before being introduced to service, especially regarding correct application of mTLS.
- More reliable application of zone settings to monitoring requests, including
- Authenticated Origin Pulls
- Aegis Egress IP Pools
- Argo Smart Routing
- HTTP/2 to Origin
- Improved support and bug fixes for retries, redirects, and proxied origin resolution
- Improved performance and reliability of monitoring requests withing the Cloudflare network
- Unrelated CDN or WAF configuration changes should have no risk of impact to pool health
- More reliable application of zone settings to monitoring requests, including
Radar now introduces Certificate Transparency (CT) insights, providing visibility into certificate issuance trends based on Certificate Transparency logs currently monitored by Cloudflare.
The following API endpoints are now available:
/ct/timeseries: Retrieves certificate issuance time series./ct/summary/{dimension}: Retrieves certificate distribution by dimension./ct/timeseries_groups/{dimension}: Retrieves time series of certificate distribution by dimension./ct/authorities: Lists certification authorities./ct/authorities/{ca_slug}: Retrieves details about a Certification Authority (CA). CA information is derived from the Common CA Database (CCADB) ↗./ct/logs: Lists CT logs./ct/logs/{log_slug}: Retrieves details about a CT log. CT log information is derived from the Google Chrome log list ↗.
For the
summaryandtimeseries_groupsendpoints, the following dimensions are available (and also usable as filters):ca: Certification Authority (certificate issuer)ca_owner: Certification Authority Ownerduration: Certificate validity duration (between NotBefore and NotAfter dates)entry_type: Entry type (certificate vs. pre-certificate)expiration_status: Expiration status (valid vs. expired)has_ips: Presence of IP addresses in certificate Subject Alternative Names (SANs) ↗has_wildcards: Presence of wildcard DNS names in certificate SANslog: CT log namelog_api: CT log API (RFC6962 ↗ vs. Static ↗)log_operator: CT log operatorpublic_key_algorithm: Public key algorithm of certificate's keysignature_algorithm: Signature algorithm used by CA to sign certificatetld: Top-level domain for DNS names found in certificates SANsvalidation_level: Validation level ↗
Check out the new Certificate Transparency insights in the new Radar page ↗.
The latest releases of @cloudflare/agents ↗ brings major improvements to MCP transport protocols support and agents connectivity. Key updates include:
MCP servers can now request user input during tool execution, enabling interactive workflows like confirmations, forms, and multi-step processes. This feature uses durable storage to preserve elicitation state even during agent hibernation, ensuring seamless user interactions across agent lifecycle events.
TypeScript // Request user confirmation via elicitationconst confirmation = await this.elicitInput({message: `Are you sure you want to increment the counter by ${amount}?`,requestedSchema: {type: "object",properties: {confirmed: {type: "boolean",title: "Confirm increment",description: "Check to confirm the increment",},},required: ["confirmed"],},});Check out our demo ↗ to see elicitation in action.
MCP now supports HTTP streamable transport which is recommended over SSE. This transport type offers:
- Better performance: More efficient data streaming and reduced overhead
- Improved reliability: Enhanced connection stability and error recover- Automatic fallback: If streamable transport is not available, it gracefully falls back to SSE
TypeScript export default MyMCP.serve("/mcp", {binding: "MyMCP",});The SDK automatically selects the best available transport method, gracefully falling back from streamable-http to SSE when needed.
Significant improvements to MCP server connections and transport reliability:
- Auto transport selection: Automatically determines the best transport method, falling back from streamable-http to SSE as needed
- Improved error handling: Better connection state management and error reporting for MCP servers
- Reliable prop updates: Centralized agent property updates ensure consistency across different contexts
You can use
.queue()to enqueue background work — ideal for tasks like processing user messages, sending notifications etc.TypeScript class MyAgent extends Agent {doSomethingExpensive(payload) {// a long running process that you want to run in the background}queueSomething() {await this.queue("doSomethingExpensive", somePayload); // this will NOT block further execution, and runs in the backgroundawait this.queue("doSomethingExpensive", someOtherPayload); // the callback will NOT run until the previous callback is complete// ... call as many times as you want}}Want to try it yourself? Just define a method like processMessage in your agent, and you’re ready to scale.
Want to build an AI agent that can receive and respond to emails automatically? With the new email adapter and onEmail lifecycle method, now you can.
TypeScript export class EmailAgent extends Agent {async onEmail(email: AgentEmail) {const raw = await email.getRaw();const parsed = await PostalMime.parse(raw);// create a response based on the email contents// and then send a replyawait this.replyToEmail(email, {fromName: "Email Agent",body: `Thanks for your email! You've sent us "${parsed.subject}". We'll process it shortly.`,});}}You route incoming mail like this:
TypeScript export default {async email(email, env) {await routeAgentEmail(email, env, {resolver: createAddressBasedEmailResolver("EmailAgent"),});},};You can find a full example here ↗.
Custom methods are now automatically wrapped with the agent's context, so calling
getCurrentAgent()should work regardless of where in an agent's lifecycle it's called. Previously this would not work on RPC calls, but now just works out of the box.TypeScript export class MyAgent extends Agent {async suggestReply(message) {// getCurrentAgent() now correctly works, even when called inside an RPC methodconst { agent } = getCurrentAgent()!;return generateText({prompt: `Suggest a reply to: "${message}" from "${agent.name}"`,tools: [replyWithEmoji],});}}Try it out and tell us what you build!
We’ve shipped a major release for the @cloudflare/sandbox ↗ SDK, turning it into a full-featured, container-based execution platform that runs securely on Cloudflare Workers.
This update adds live streaming of output, persistent Python and JavaScript code interpreters with rich output support (charts, tables, HTML, JSON), file system access, Git operations, full background process control, and the ability to expose running services via public URLs.
This makes it ideal for building AI agents, CI runners, cloud REPLs, data analysis pipelines, or full developer tools — all without managing infrastructure.
Create persistent code contexts with support for rich visual + structured outputs.
Creates a new code execution context with persistent state.
TypeScript // Create a Python contextconst pythonCtx = await sandbox.createCodeContext({ language: "python" });// Create a JavaScript contextconst jsCtx = await sandbox.createCodeContext({ language: "javascript" });Options:
- language: Programming language ('python' | 'javascript' | 'typescript')
- cwd: Working directory (default: /workspace)
- envVars: Environment variables for the context
Executes code with optional streaming callbacks.
TypeScript // Simple executionconst execution = await sandbox.runCode('print("Hello World")', {context: pythonCtx,});// With streaming callbacksawait sandbox.runCode(`for i in range(5):print(f"Step {i}")time.sleep(1)`,{context: pythonCtx,onStdout: (output) => console.log("Real-time:", output.text),onResult: (result) => console.log("Result:", result),},);Options:
- language: Programming language ('python' | 'javascript' | 'typescript')
- cwd: Working directory (default: /workspace)
- envVars: Environment variables for the context
Returns a streaming response for real-time processing.
TypeScript const stream = await sandbox.runCodeStream("import time; [print(i) for i in range(10)]",);// Process the stream as neededInterpreter outputs are auto-formatted and returned in multiple formats:
- text
- html (e.g., Pandas tables)
- png, svg (e.g., Matplotlib charts)
- json (structured data)
- chart (parsed visualizations)
TypeScript const result = await sandbox.runCode(`import seaborn as snsimport matplotlib.pyplot as pltdata = sns.load_dataset("flights")pivot = data.pivot("month", "year", "passengers")sns.heatmap(pivot, annot=True, fmt="d")plt.title("Flight Passengers")plt.show()pivot.to_dict()`,{ context: pythonCtx },);if (result.png) {console.log("Chart output:", result.png);}Start background processes and expose them with live URLs.
TypeScript await sandbox.startProcess("python -m http.server 8000");const preview = await sandbox.exposePort(8000);console.log("Live preview at:", preview.url);Start, inspect, and terminate long-running background processes.
TypeScript const process = await sandbox.startProcess("node server.js");console.log(`Started process ${process.id} with PID ${process.pid}`);// Monitor the processconst logStream = await sandbox.streamProcessLogs(process.id);for await (const log of parseSSEStream<LogEvent>(logStream)) {console.log(`Server: ${log.data}`);}- listProcesses() - List all running processes
- getProcess(id) - Get detailed process status
- killProcess(id, signal) - Terminate specific processes
- killAllProcesses() - Kill all processes
- streamProcessLogs(id, options) - Stream logs from running processes
- getProcessLogs(id) - Get accumulated process output
Clone Git repositories directly into the sandbox.
TypeScript await sandbox.gitCheckout("https://github.com/user/repo", {branch: "main",targetDir: "my-project",});Sandboxes are still experimental. We're using them to explore how isolated, container-like workloads might scale on Cloudflare — and to help define the developer experience around them.
We're thrilled to be a Day 0 partner with OpenAI ↗ to bring their latest open models ↗ to Workers AI, including support for Responses API, Code Interpreter, and Web Search (coming soon).
Get started with the new models at
@cf/openai/gpt-oss-120band@cf/openai/gpt-oss-20b. Check out the blog ↗ for more details about the new models, and thegpt-oss-120bandgpt-oss-20bmodel pages for more information about pricing and context windows.If you call the model through:
- Workers Binding, it will accept/return Responses API –
env.AI.run(“@cf/openai/gpt-oss-120b”) - REST API on
/runendpoint, it will accept/return Responses API –https://api.cloudflare.com/client/v4/accounts/<account_id>/ai/run/@cf/openai/gpt-oss-120b - REST API on new
/responsesendpoint, it will accept/return Responses API –https://api.cloudflare.com/client/v4/accounts/<account_id>/ai/v1/responses - REST API for OpenAI Compatible endpoint, it will return Chat Completions (coming soon) –
https://api.cloudflare.com/client/v4/accounts/<account_id>/ai/v1/chat/completions
curl https://api.cloudflare.com/client/v4/accounts/<account_id>/ai/v1/responses \-H "Content-Type: application/json" \-H "Authorization: Bearer $CLOUDFLARE_API_KEY" \-d '{"model": "@cf/openai/gpt-oss-120b","reasoning": {"effort": "medium"},"input": [{"role": "user","content": "What are the benefits of open-source models?"}]}'The model is natively trained to support stateful code execution, and we've implemented support for this feature using our Sandbox SDK ↗ and Containers ↗. Cloudflare's Developer Platform is uniquely positioned to support this feature, so we're very excited to bring our products together to support this new use case.
We are working to implement Web Search for the model, where users can bring their own Exa API Key so the model can browse the Internet.
- Workers Binding, it will accept/return Responses API –
As part of the ongoing open beta for Workers Builds, we’ve increased the available disk space for builds from 8 GB to 20 GB for both Free and Paid plans.
This provides more space for larger projects, dependencies, and build artifacts while improving overall build reliability.
Metric Free Plan Paid Plans Disk Space 20 GB 20 GB All other build limits — including CPU, memory, build minutes, and timeout remain unchanged.
This week's highlight focuses on a series of significant vulnerabilities identified across widely adopted web platforms, from enterprise-grade CMS to essential backend administration tools. The findings reveal multiple vectors for attack, including critical flaws that allow for full server compromise and others that enable targeted attacks against users.
Key Findings
-
Sitecore (CVE-2025-34509, CVE-2025-34510, CVE-2025-34511): A hardcoded credential allows remote attackers to access administrative APIs. Once authenticated, they can exploit an additional vulnerability to upload arbitrary files, leading to remote code execution.
-
Grafana (CVE-2025-4123): A cross-site scripting (XSS) vulnerability allows an attacker to redirect users to a malicious website, which can then execute arbitrary JavaScript in the victim's browser.
-
LaRecipe (CVE-2025-53833): Through Server-Side Template Injection, attackers can execute arbitrary commands on the server, potentially access sensitive environment variables, and escalate access depending on server configuration.
-
CentOS WebPanel (CVE-2025-48703): A command injection vulnerability could allow a remote attacker to execute arbitrary commands on the server.
-
WordPress (CVE-2023-5561): This vulnerability allows unauthenticated attackers to determine the email addresses of users who have published public posts on an affected website.
-
WordPress Plugin - WPBookit (CVE-2025-6058): A missing file type validation allows unauthenticated attackers to upload arbitrary files to the server, creating the potential for remote code execution.
-
WordPress Theme - Motors (CVE-2025-4322): Due to improper identity validation, an unauthenticated attacker can change the passwords of arbitrary users, including administrators, to gain access to their accounts.
Impact
These vulnerabilities pose a multi-layered threat to widely adopted web technologies, ranging from enterprise-grade platforms like Sitecore to everyday solutions such as WordPress, and backend tools like CentOS WebPanel. The most severe risks originate in remote code execution (RCE) flaws found in Sitecore, CentOS WebPanel, LaRecipe, and the WPBookit plugin. These allow attackers to bypass security controls and gain deep access to the server, enabling them to steal sensitive data, deface websites, install persistent malware, or use the compromised server as a launchpad for further attacks.
The privilege escalation vulnerability is the Motors theme, which allows for a complete administrative account takeover on WordPress sites. This effectively hands control of the application to an attacker, who can then manipulate content, exfiltrate user data, and alter site functionality without needing to breach the server itself.
The Grafana cross-site scripting (XSS) flaw can be used to hijack authenticated user sessions or steal credentials, turning a trusted user's browser into an attack vector.
Meanwhile, the information disclosure flaw in WordPress core provides attackers with valid user emails, fueling targeted phishing campaigns that aim to secure the same account access achievable through the other exploits.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100535A Sitecore - Dangerous File Upload - CVE:CVE-2025-34510, CVE:CVE-2025-34511 Log Block This is a New Detection Cloudflare Managed Ruleset 100535 Sitecore - Information Disclosure - CVE:CVE-2025-34509 Log Block This is a New Detection Cloudflare Managed Ruleset 100543 Grafana - Directory Traversal - CVE:CVE-2025-4123 Log Block This is a New Detection Cloudflare Managed Ruleset 100545 WordPress - Information Disclosure - CVE:CVE-2023-5561 Log Block This is a New Detection Cloudflare Managed Ruleset 100820 CentOS WebPanel - Remote Code Execution - CVE:CVE-2025-48703 Log Block This is a New Detection Cloudflare Managed Ruleset 100821 LaRecipe - SSTI - CVE:CVE-2025-53833 Log Block This is a New Detection Cloudflare Managed Ruleset 100822 WordPress:Plugin:WPBookit - Remote Code Execution - CVE:CVE-2025-6058 Log Block This is a New Detection Cloudflare Managed Ruleset 100823 WordPress:Theme:Motors - Privilege Escalation - CVE:CVE-2025-4322 Log Block This is a New Detection -
Earlier this year, we announced the launch of the new Terraform v5 Provider. We are aware of the high mumber of issues ↗ reported by the Cloudflare community related to the v5 release. We have committed to releasing improvements on a 2 week cadeance to ensure it's stability and reliability. We have also pivoted from an issue-to-issue approach to a resource-per-resource approach - we will be focusing on specific resources for every release, stablizing the release and closing all associated bugs with that resource before moving onto resolving migration issues.
Thank you for continuing to raise issues. We triage them weekly and they help make our products stronger.
- Resources stablized:
cloudflare_custom_pagescloudflare_page_rulecloudflare_dns_recordcloudflare_argo_tiered_caching
- Addressed chronic drift issues in
cloudflare_logpush_job,cloudflare_zero_trust_dns_location,cloudflare_ruleset&cloudflare_api_token cloudflare_zone_subscriptonreturns expected valuesrate_plan.idfrom former versionscloudflare_workers_scriptcan now successfully be destroyed with bindings & migration for Durable Objects now recorded in tfstate- Ability to configure
add_headersundercloudflare_zero_trust_gateway_policy - Other bug fixes
For a more detailed look at all of the changes, see the changelog ↗ in GitHub.
- #5666: cloudflare_ruleset example lists id which is a read-only field ↗
- #5578: cloudflare_logpush_job plan always suggests changes ↗
- #5552: 5.4.0: Since provider update, existing cloudflare_list_item would be recreated "created" state ↗
- #5670: cloudflare_zone_subscription: uses wrong ID field in Read/Update ↗
- #5548: cloudflare_api_token resource always shows changes (drift) ↗
- #5634: cloudflare_workers_script with bindings fails to be destroyed ↗
- #5616: cloudflare_workers_script Unable to deploy worker assets ↗
- #5331: cloudflare_workers_script 500 internal server error when uploading python ↗
- #5701: cloudflare_workers_script migrations for Durable Objects not recorded in tfstate; cannot be upgraded between versions ↗
- #5704: cloudflare_workers_script randomly fails to deploy when changing compatibility_date ↗
- #5439: cloudflare_workers_script (v5.2.0) ignoring content and bindings properties ↗
- #5522: cloudflare_workers_script always detects changes after apply ↗
- #5693: cloudflare_zero_trust_access_identity_provider gives recurring change on OTP pin login ↗
- #5567: cloudflare_r2_custom_domain doesn't roundtrip jurisdiction properly ↗
- #5179: Bad request with when creating cloudflare_api_shield_schema resource ↗
If you have an unaddressed issue with the provider, we encourage you to check the open issues ↗ and open a new one if one does not already exist for what you are experiencing.
We suggest holding off on migration to v5 while we work on stablization. This help will you avoid any blocking issues while the Terraform resources are actively being stablized.
If you'd like more information on migrating from v4 to v5, please make use of the migration guide ↗. We have provided automated migration scripts using Grit which simplify the transition, although these do not support implementations which use Terraform modules, so customers making use of modules need to migrate manually. Please make use of
terraform planto test your changes before applying, and let us know if you encounter any additional issues by reporting to our GitHub repository ↗.- Resources stablized:
You can now configure and run Containers alongside your Worker during local development when using the Cloudflare Vite plugin. Previously, you could only develop locally when using Wrangler as your local development server.
You can simply configure your Worker and your Container(s) in your Wrangler configuration file:
{"name": "container-starter","main": "src/index.js","containers": [{"class_name": "MyContainer","image": "./Dockerfile","instances": 5}],"durable_objects": {"bindings": [{"class_name": "MyContainer","name": "MY_CONTAINER"}]},"migrations": [{"new_sqlite_classes": ["MyContainer"],"tag": "v1"}],}name = "container-starter"main = "src/index.js"[[containers]]class_name = "MyContainer"image = "./Dockerfile"instances = 5[[durable_objects.bindings]]class_name = "MyContainer"name = "MY_CONTAINER"[[migrations]]new_sqlite_classes = [ "MyContainer" ]tag = "v1"Once your Worker and Containers are configured, you can access the Container instances from your Worker code:
TypeScript import { Container, getContainer } from "@cloudflare/containers";export class MyContainer extends Container {defaultPort = 4000; // Port the container is listening onsleepAfter = "10m"; // Stop the instance if requests not sent for 10 minutes}async fetch(request, env) {const { "session-id": sessionId } = await request.json();// Get the container instance for the given session IDconst containerInstance = getContainer(env.MY_CONTAINER, sessionId)// Pass the request to the container instance on its default portreturn containerInstance.fetch(request);}To develop your Worker locally, start a local dev server by running
Terminal window vite devin your terminal.
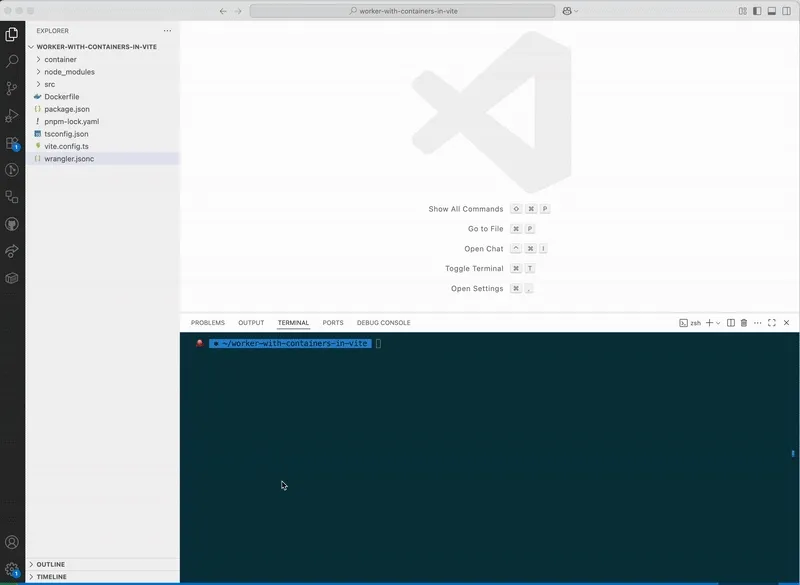
Learn more about Cloudflare Containers ↗ or the Cloudflare Vite plugin ↗ in our developer docs.
The Cloudflare Terraform provider resources for Cloudflare WAN tunnels and routes now support Terraform provider version 5. Customers using infrastructure-as-code workflows can manage their tunnel and route configuration with the latest provider version.
For more information, refer to the Cloudflare Terraform provider documentation ↗.
Today, we are excited to announce that all Magic Transit and Magic WAN customers with CMB EU (Customer Metadata Boundary - Europe) enabled in their account will be able to access GRE, IPsec, and CNI health check and traffic volume data in the Cloudflare dashboard and via API.
This ensures that all Magic Transit and Magic WAN customers with CMB EU enabled will be able to access all Magic Transit and Magic WAN features.
Specifically, these two GraphQL endpoints are now compatible with CMB EU:
magicTransitTunnelHealthChecksAdaptiveGroupsmagicTransitTunnelTrafficAdaptiveGroups
Any template which uses Worker environment variables, secrets, or Secrets Store secrets can now be deployed using a Deploy to Cloudflare button.
Define environment variables and secrets store bindings in your Wrangler configuration file as normal:
{"name": "my-worker","main": "./src/index.ts",// Set this to today's date"compatibility_date": "2026-03-12","vars": {"API_HOST": "https://example.com",},"secrets_store_secrets": [{"binding": "API_KEY","store_id": "demo","secret_name": "api-key"}]}name = "my-worker"main = "./src/index.ts"# Set this to today's datecompatibility_date = "2026-03-12"[vars]API_HOST = "https://example.com"[[secrets_store_secrets]]binding = "API_KEY"store_id = "demo"secret_name = "api-key"Add secrets to a
.dev.vars.exampleor.env.examplefile:.dev.vars.example COOKIE_SIGNING_KEY=my-secret # commentAnd optionally, you can add a description for these bindings in your template's
package.jsonto help users understand how to configure each value:package.json {"name": "my-worker","private": true,"cloudflare": {"bindings": {"API_KEY": {"description": "Select your company's API key for connecting to the example service."},"COOKIE_SIGNING_KEY": {"description": "Generate a random string using `openssl rand -hex 32`."}}}}These secrets and environment variables will be presented to users in the dashboard as they deploy this template, allowing them to configure each value. Additional information about creating templates and Deploy to Cloudflare buttons can be found in our documentation.
The Audit Logs v2 UI is now available to all Cloudflare customers in Beta. This release builds on the public Beta of the Audit Logs v2 API and introduces a redesigned user interface with powerful new capabilities to make it easier to investigate account activity.
Enabling the new UI
To try the new user interface, go to Manage Account > Audit Logs. The previous version of Audit Logs remains available and can be re-enabled at any time using the Switch back to old Audit Logs link in the banner at the top of the page.
New Features:
- Advanced Filtering: Filter logs by actor, resource, method, and more for faster insights.
- On-hover filter controls: Easily include or exclude values in queries by hovering over fields within a log entry.
- Detailed Log Sidebar: View rich context for each log entry without leaving the main view.
- JSON Log View: Inspect the raw log data in a structured JSON format.
- Custom Time Ranges: Define your own time windows to view historical activity.
- Infinite Scroll: Seamlessly browse logs without clicking through pages.
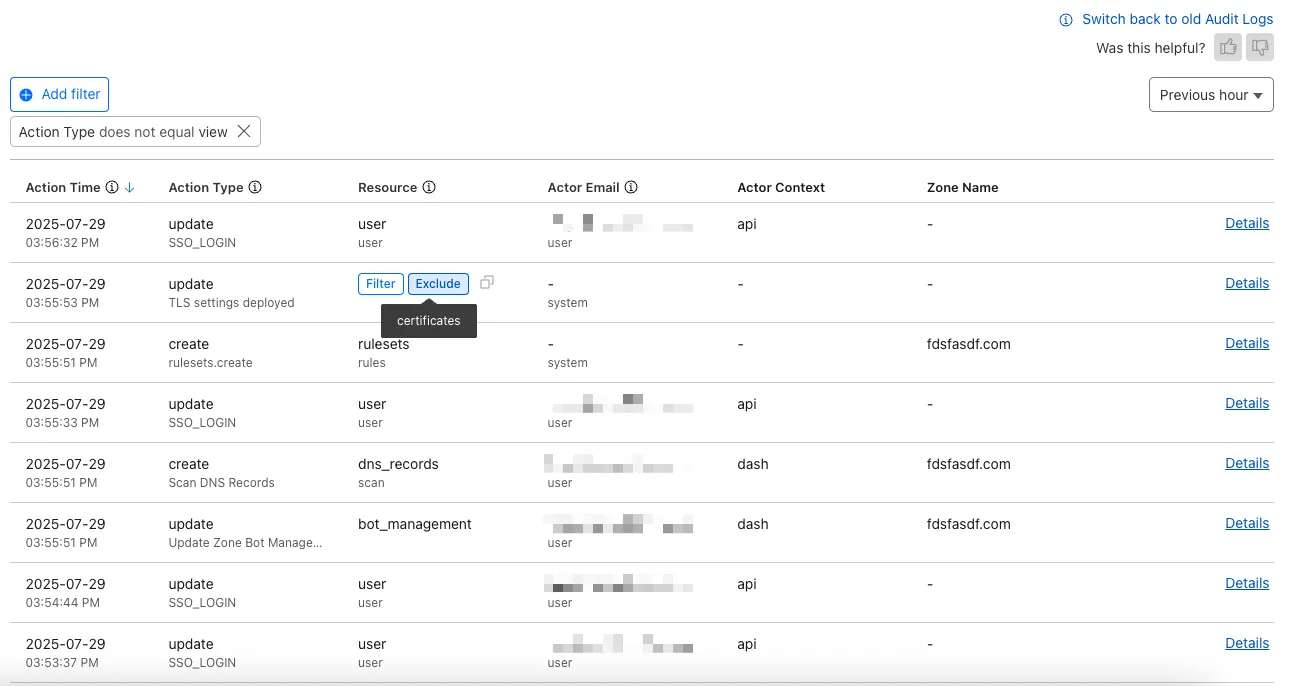
For more details on Audit Logs v2, see the Audit Logs documentation ↗.
Known issues
- A small number of audit logs may currently be unavailable in Audit Logs v2. In some cases, certain fields such as actor information may be missing in certain audit logs. We are actively working to improve coverage and completeness for General Availability.
- Export to CSV is not supported in the new UI.
We are actively refining the Audit Logs v2 experience and welcome your feedback. You can share overall feedback by clicking the thumbs up or thumbs down icons at the top of the page, or provide feedback on specific audit log entries using the thumbs icons next to each audit log line or by filling out our feedback form ↗.
We’ve launched pricing for Browser Rendering, including a free tier and a pay-as-you-go model that scales with your needs. Starting August 20, 2025, Cloudflare will begin billing for Browser Rendering.
There are two ways to use Browser Rendering. Depending on the method you use, here’s how billing will work:
- REST API: Charged for Duration only ($/browser hour)
- Workers Bindings: Charged for both Duration and Concurrency ($/browser hour and # of concurrent browsers)
Included usage and pricing by plan
Plan Included duration Included concurrency Price (beyond included) Workers Free 10 minutes per day 3 concurrent browsers N/A Workers Paid 10 hours per month 10 concurrent browsers (averaged monthly) 1. REST API: $0.09 per additional browser hour
2. Workers Bindings: $0.09 per additional browser hour
$2.00 per additional concurrent browserWhat you need to know:
- Workers Free Plan: 10 minutes of browser usage per day with 3 concurrent browsers at no charge.
- Workers Paid Plan: 10 hours of browser usage per month with 10 concurrent browsers (averaged monthly) at no charge. Additional usage is charged as shown above.
You can monitor usage via the Cloudflare dashboard ↗. Go to Compute (Workers) > Browser Rendering.
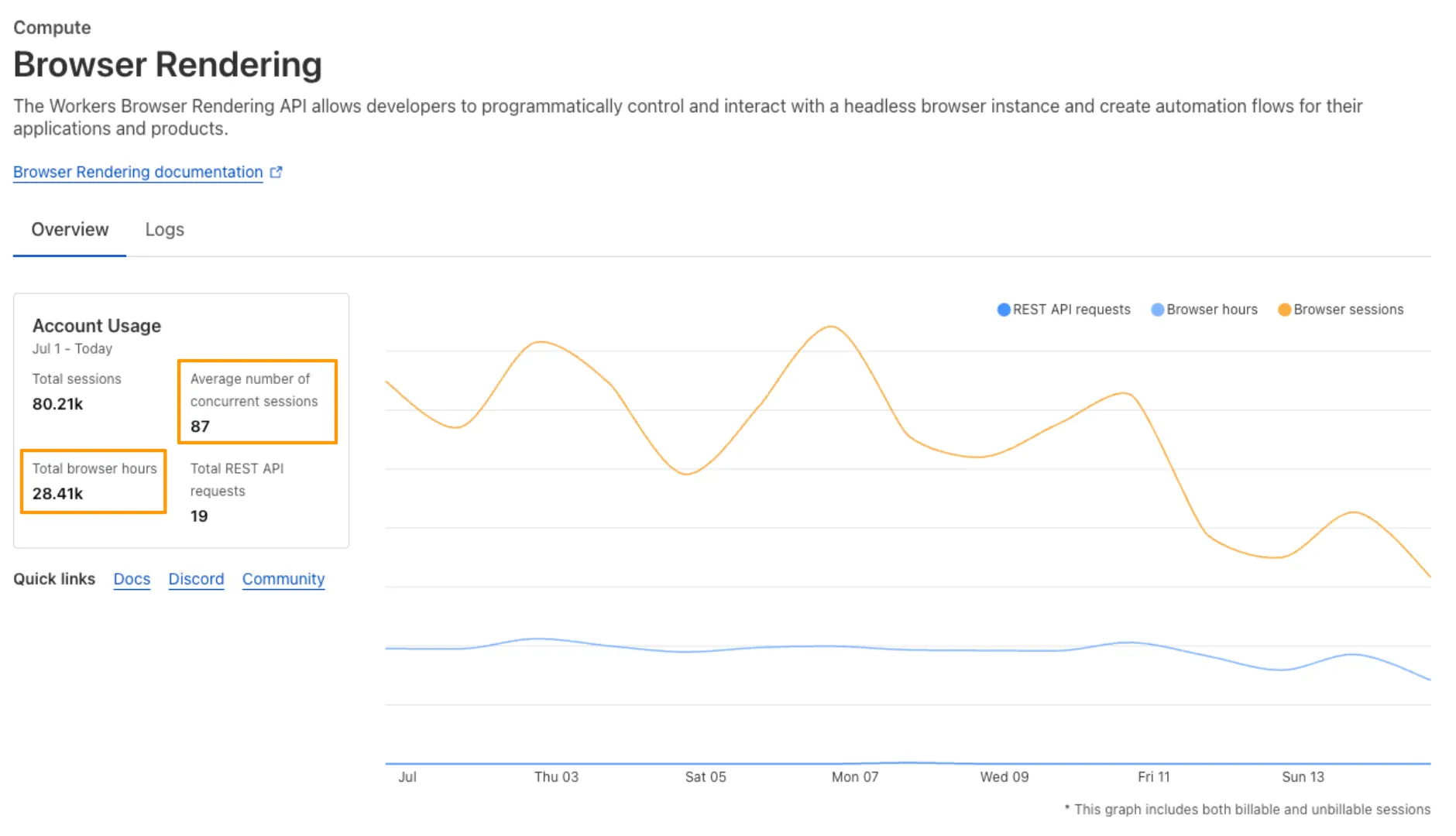
If you've been using Browser Rendering and do not wish to incur charges, ensure your usage stays within your plan's included usage. To estimate costs, take a look at these example pricing scenarios.
We have introduced a new Security Threat category called Scam. Relevant domains are marked with the Scam category. Scam typically refers to fraudulent websites and schemes designed to trick victims into giving away money or personal information.
New category added
Parent ID Parent Name Category ID Category Name 21 Security Threats 191 Scam Refer to Gateway domain categories to learn more.
This week’s update spotlights several vulnerabilities across Apache Tomcat, MongoDB, and Fortinet FortiWeb. Several flaws related with a memory leak in Apache Tomcat can lead to a denial-of-service attack. Additionally, a code injection flaw in MongoDB's Mongoose library allows attackers to bypass security controls to access restricted data.
Key Findings
-
Fortinet FortiWeb (CVE-2025-25257): An improper neutralization of special elements used in a SQL command vulnerability in Fortinet FortiWeb versions allows an unauthenticated attacker to execute unauthorized SQL code or commands.
-
Apache Tomcat (CVE-2025-31650): A improper Input Validation vulnerability in Apache Tomcat that could create memory leak when incorrect error handling for some invalid HTTP priority headers resulted in incomplete clean-up of the failed request.
-
MongoDB (CVE-2024-53900, CVE:CVE-2025-23061): Improper use of
$wherein match and a nested$wherefilter with apopulate()match in Mongoose can lead to search injection.
Impact
These vulnerabilities target user-facing components, web application servers, and back-end databases. A SQL injection flaw in Fortinet FortiWeb can lead to data theft or system compromise. A separate issue in Apache Tomcat involves a memory leak from improper input validation, which could be exploited for a denial-of-service (DoS) attack. Finally, a vulnerability in MongoDB's Mongoose library allows attackers to bypass security filters and access unauthorized data through malicious search queries.
Ruleset Rule ID Legacy Rule ID Description Previous Action New Action Comments Cloudflare Managed Ruleset 100804 BerriAI - SSRF - CVE:CVE-2024-6587 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100812 Fortinet FortiWeb - Remote Code Execution - CVE:CVE-2025-25257 Log Block This is a New Detection Cloudflare Managed Ruleset 100813 Apache Tomcat - DoS - CVE:CVE-2025-31650 Log Disabled This is a New Detection Cloudflare Managed Ruleset 100815 MongoDB - Remote Code Execution - CVE:CVE-2024-53900, CVE:CVE-2025-23061 Log Block This is a New Detection Cloudflare Managed Ruleset 100816 MongoDB - Remote Code Execution - CVE:CVE-2024-53900, CVE:CVE-2025-23061 Log Block This is a New Detection -
A new Beta release for the Windows WARP client is now available on the beta releases downloads page.
This release contains minor fixes and improvements.
Changes and improvements
- Improvements to better manage multi-user pre-login registrations.
- Fixed an issue preventing devices from reaching split-tunneled traffic even when WARP was disconnected.
- Fix to prevent WARP from re-enabling its firewall rules after a user-initiated disconnect.
- Improvement to managed network detection checks for faster switching between managed networks.
Known issues
For Windows 11 24H2 users, Microsoft has confirmed a regression that may lead to performance issues like mouse lag, audio cracking, or other slowdowns. Cloudflare recommends users experiencing these issues upgrade to a minimum Windows 11 24H2 version KB5062553 or higher for resolution.
Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
Devices with
KB5055523installed may receive a warning aboutWin32/ClickFix.ABAbeing present in the installer. To resolve this false positive, update Microsoft Security Intelligence to version 1.429.19.0 or later.DNS resolution may be broken when the following conditions are all true:
- WARP is in Secure Web Gateway without DNS filtering (tunnel-only) mode.
- A custom DNS server address is configured on the primary network adapter.
- The custom DNS server address on the primary network adapter is changed while WARP is connected.
To work around this issue, reconnect the WARP client by toggling off and back on.
A new Beta release for the macOS WARP client is now available on the beta releases downloads page.
This release contains minor fixes and improvements.
Changes and improvements
- Fixed an issue preventing devices from reaching split-tunneled traffic even when WARP was disconnected.
- Fix to prevent WARP from re-enabling its firewall rules after a user-initiated disconnect.
- Improvement to managed network detection checks for faster switching between managed networks.
Known issues
- macOS Sequoia: Due to changes Apple introduced in macOS 15.0.x, the WARP client may not behave as expected. Cloudflare recommends the use of macOS 15.4 or later.
- Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
Gateway can now apply HTTP filtering to all proxied HTTP requests, not just traffic on standard HTTP (
80) and HTTPS (443) ports. This means all requests can now be filtered by A/V scanning, file sandboxing, Data Loss Prevention (DLP), and more.You can turn this setting on by going to Settings > Network > Firewall and choosing Inspect on all ports.
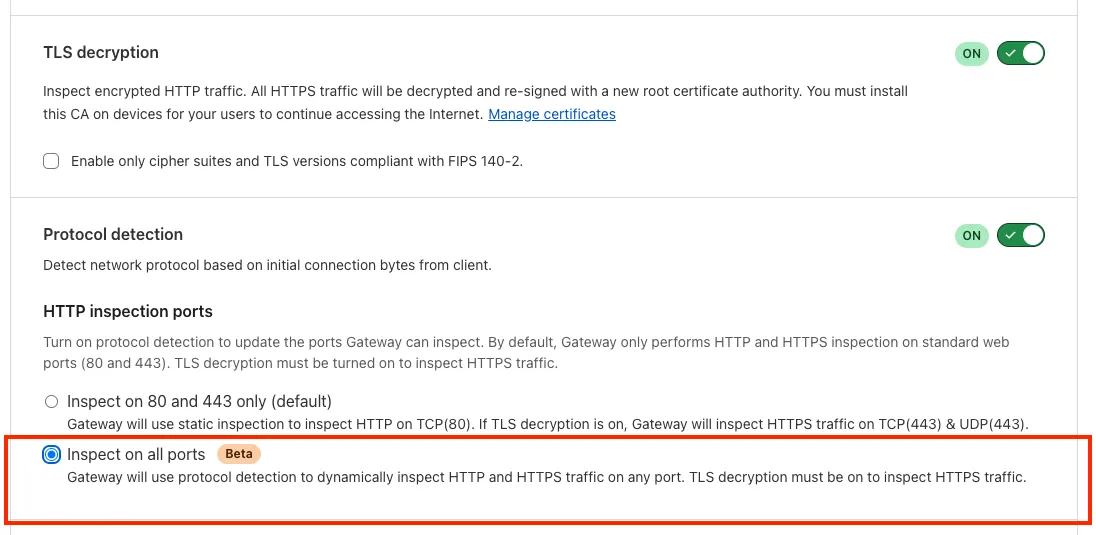
To learn more, refer to Inspect on all ports (Beta).
A new GA release for the Windows WARP client is now available on the stable releases downloads page.
This release contains minor fixes and improvements.
Changes and improvements
- WARP proxy mode now uses the operating system's DNS settings. Changes made to system DNS settings while in proxy mode require the client to be turned off then back on to take effect.
- Changes to the SCCM VPN boundary support feature to no longer restart the SMS Agent Host (
ccmexec.exe) service. - Fixed an issue affecting clients in Split Tunnel Include mode, where access to split-tunneled traffic was blocked after reconnecting the client.
Known issues
For Windows 11 24H2 users, Microsoft has confirmed a regression that may lead to performance issues like mouse lag, audio cracking, or other slowdowns. Cloudflare recommends users experiencing these issues upgrade to a minimum Windows 11 24H2 version KB5062553 or higher for resolution.
Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
Devices with
KB5055523installed may receive a warning aboutWin32/ClickFix.ABAbeing present in the installer. To resolve this false positive, update Microsoft Security Intelligence to version 1.429.19.0 or later.DNS resolution may be broken when the following conditions are all true:
- WARP is in Secure Web Gateway without DNS filtering (tunnel-only) mode.
- A custom DNS server address is configured on the primary network adapter.
- The custom DNS server address on the primary network adapter is changed while WARP is connected.
To work around this issue, reconnect the WARP client by toggling off and back on.
A new GA release for the macOS WARP client is now available on the stable releases downloads page.
This release contains minor fixes and improvements.
Changes and improvements
- WARP proxy mode now uses the operating system's DNS settings. Changes made to system DNS settings while in proxy mode require the client to be turned off then back on to take effect.
- Fixed an issue affecting clients in Split Tunnel Include mode, where access to split-tunneled traffic was blocked after reconnecting the client.
- For macOS deployments, the WARP client can now be managed using an
mdm.xmlfile placed in/Library/Application Support/Cloudflare/mdm.xml. This new configuration option offers an alternative to the still supported method of deploying a managed plist through an MDM solution.
Known issues
- macOS Sequoia: Due to changes Apple introduced in macOS 15.0.x, the WARP client may not behave as expected. Cloudflare recommends the use of macOS 15.4 or later.
- Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.
A new GA release for the Linux WARP client is now available on the stable releases downloads page.
This release contains minor fixes and improvements.
Changes and improvements
- WARP proxy mode now uses the operating system's DNS settings. Changes made to system DNS settings while in proxy mode require the client to be turned off then back on to take effect.
- Fixed an issue affecting clients in Split Tunnel Include mode, where access to split-tunneled traffic was blocked after reconnecting the client.
Known issues
- Devices using WARP client 2025.4.929.0 and up may experience Local Domain Fallback failures if a fallback server has not been configured. To configure a fallback server, refer to Route traffic to fallback server.